DNS + its Security Risks
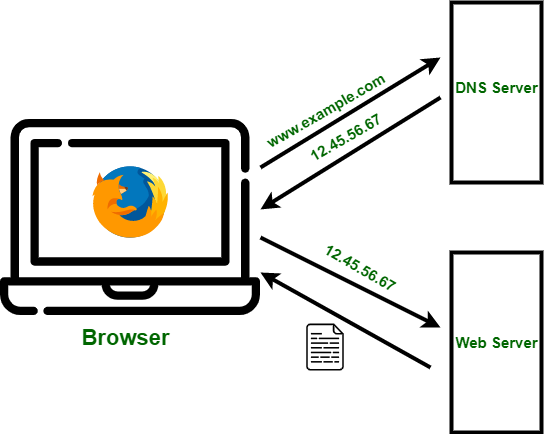
DNS stands for “Domain Name System”. A domain name is like the translated, human-friendly version of an IP address: “google.com”, for example. IP addresses are “unique addresses that identify devices connected to the internet or local networks” and they look somewhat like this: “xxx.xx.x.xx.” In the diagram below, the relationship between IP address and domain is outlined pretty clearly.
A huge risk associated with DNS is something called “typosquatting”; Typosquatting is when people buy domain names that are purposefully incredibly similar to popular, trustworthy domain names that are frequently interacted with by users, in hopes that they press one wrong key and are directed to an alternate site where cybercriminals are able to steal your information or install malware onto your device. Typosquatting is a remarkably easy cyber attack to carry out, since all you have to do is purchase an available domain. This does not change the fact that this is still a very effective form of attack that poses a viable risk to users.
A typosquatting attack for a website looks somewhat like this: google.com is the desired website, goggle.com or even google.org is the hacker’s domain. For emails, it can look like this: user@yahooo.com vs. user@yahoo.com
Effects
Security researchers performed an experiment with typosquatting email addresses of S&P 500 companies by removing a period in the address, and successfully obtained over 120,000 corporate emails including many with sensitive information. The DNS risk of typosquatting is intertwined with user error, so solutions have been a little difficult to come by. Many large companies have been hit with these types of attacks, most famously google.com vs goggle.com, but also airfrance.com was hit with a arifrance.com attack.

Solutions
There are effective ways to protect against the dangers of typosquatting. A company can protect against this by paying to trademark their domain name, and purchasing any domains remotely similar so simple user misspellings are less dangerous. As users, we can be very intentional and careful when typing in a URL because a wrong key press can install hazardous malware on your device. These risks are particularly serious with medium-sized and small-sized companies, as they might not have the resources to buy up every possible misspelling of their domain name to keep their consumers safe. Other ways to protect against this threat is to use resources like DNS twist, which search through domain databases to see if there might already be fake domains (with similar spellings, etc) created to steal traffic. Another way to stay ahead of typosquatting is to frequently monitor the traffic on your website for a rapid decrease in traffic because this is a telltale sign of this kind of cyberattack. DNS is a a very important, though often overlooked component of internet safety and it is imperative we protect ourselves against its areas that may pose risks.

 -https://futureboy.us/stegano/encinput.html <— the very awesome website 🙂
-https://futureboy.us/stegano/encinput.html <— the very awesome website 🙂








Recent Comments